If your company works with the United States Department of Defense—or even with a customer who does—Cybersecurity Maturity Model Certification (CMMC) is no longer theoretical. It’s active, it’s contractual, and it’s going to determine who can and cannot win defense work moving forward.
I’ve been having more conversations with clients who are realizing this certification is a requirement. The timeline is set. The expectations are clear. But for many small to mid-sized businesses, unfortunately, they aren’t prepared yet.
In this article I’ll identify why CMMC is coming into play right now, what you need to know to obtain certification, and resources that can help you in the process.
What is CMMC & Why is it important?
CMMC (Cybersecurity Maturity Model Certification) is the Department of Defense’s framework for ensuring contractors properly protect sensitive government information. Under the previous model, contractors were largely self-certified: They documented security controls and attested they were compliant. There was no required third-party validation for most organizations.
CMMC 2.0 changes that.
Depending on the level required—Level 1 or Level 2—you must now either formally attest to specific controls or undergo a third-party assessment to prove you meet them. The goal is straightforward: strengthen cybersecurity across the entire defense supply chain.
The CMMC Timeline
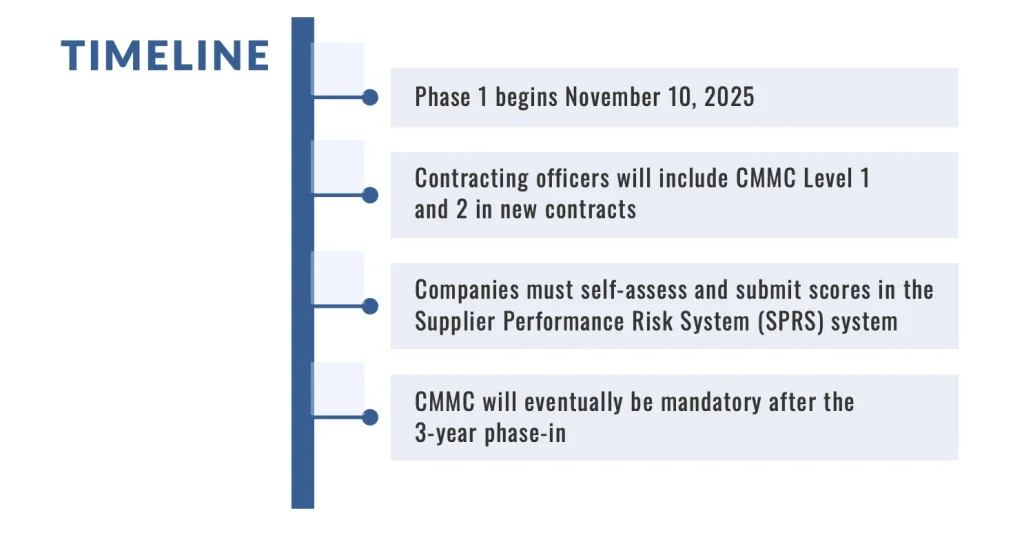
On November 10, 2025, CMMC requirements began appearing in DoD contracts. By November 2026, companies required to hold certification will not be eligible to win contracts without it. This applies to both contractors and subcontractors.
Pay attention here: Even if you don’t contract directly with the DoD, you may still be affected. If your customer is a defense contractor and shares certain types of information with you, they may require you to obtain a specific CMMC level to continue doing business together.
Level 1 vs. Level 2 Certification: What you need to know about the differences
The most important distinction in CMMC is between Level 1 and Level 2.
Level 1: Foundational Controls
- Level 1 applies to companies handling Federal Contract Information (FCI). It requires 15 basic cybersecurity practices—good security hygiene like access control and basic safeguarding measures.
- Level 1 allows for self-attestation. There is no mandatory third-party audit.
- For many smaller businesses, this level is manageable with reasonable adjustments.
Level 2: A Higher Standard
Level 2 applies to organizations who handle, process or store Controlled Unclassified Information (CUI). This includes sensitive data like technical drawings, test results, or operational details that aren’t classified but must be protected.
Level 2 requires an implementation of 110 security controls and, most notably, a formal third-party assessment.
The jump from 15 to 110 controls is substantial. For most small and mid-sized businesses, it requires new systems, new processes, and significantly improved documentation. It’s not just about having policies—it’s about proving controls are functioning through logs, reports, and audit evidence.
The Level 2 Assessment Bottleneck
One challenge that isn’t discussed enough is assessor availability for Level 2 certification. There are a limited number of authorized third-party assessment organizations, and thousands of contractors are working toward the same November 2026 deadline.
That’s why, if you anticipate needing Level 2 certification and haven’t started, you are playing a risky game the longer you wait. Preparing properly often takes 6–12 months, depending on your current environment; delaying the certification process could mean being unable to schedule an assessment in time and, ultimately, losing a contract.
Two Cybersecurity Areas That Often Require Upgrades
While Level 2 includes 110 controls, two technology areas frequently surface during gap assessments: Data Loss Prevention (DLP) and Security Service Edge (SSE).
Data Loss Prevention (DLP)
CMMC is fundamentally about protecting sensitive data, especially CUI. DLP solutions help you:
- Identify and classify sensitive files
- Monitor how data moves internally
- Prevent unauthorized sharing via email or cloud platforms
- Generate audit logs required for assessments
For example, if an employee attempts to email a sensitive technical document externally, a DLP system can block or flag that action. That level of control—and the ability to produce evidence of it—is exactly what assessors expect. For many manufacturers and engineering firms, DLP becomes a foundational component of Level 2 readiness.
Security Service Edge (SSE)
SSE addresses how users access your systems. Traditional VPN models grant broad network access once connected. CMMC aligns more closely with zero trust principles—continuous identity verification and limited access based on role. SSE platforms modernize security by:
- Enforcing identity-based access controls
- Restricting users to only what they need
- Providing centralized visibility
- Replacing fragmented VPN and firewall solutions
This approach strengthens access management and better supports Level 2 requirements.
What Every Contractor Or Subcontractor Should Be Doing Now
While most large defense contractors have established compliance teams and cybersecurity programs, most small and mid-sized businesses often do not—it might be just a few people in the office. If that sounds familiar, the move to CMMC might feel overwhelming—especially with limited internal IT resources.
However, there is a clear path forward: Start today. Companies that start early and build a clear roadmap will be in the strongest position to earn certification and ultimately win contracts.
If you’re unsure which level of CMMC applies to you, let’s have that conversation first. Contact us at Atlantic Data Systems today, and we’ll schedule an assessment of your current security posture, identify any gaps, and build a realistic plan.
CMMC is not going away. But handled correctly, it’s more than compliance—it’s an opportunity to strengthen your security, improve operational maturity, and demonstrate to customers that you take data protection seriously.
The key is simple: start now.